Your stupid brain is the biggest risk
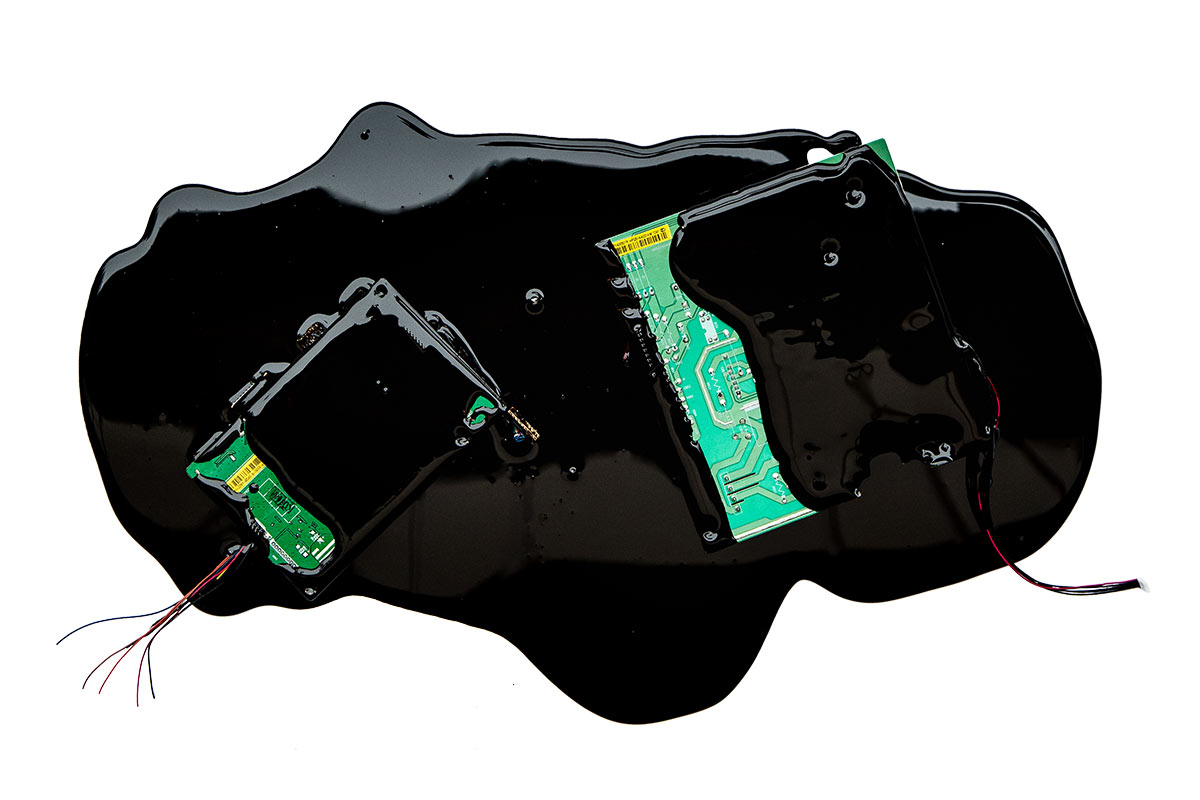
Sabotage, intelligence attack or influencing – there are several kinds of cyber threats that can clog your business. Turns out we ourselves often are the ones opening the door for the hackers.
Imagine that you are an IT administrator and you are watching your screen go black. Just like that, out of the blue. You are silently cursing and start looking around. The same is happening everywhere. One after the other the screens go black. Some of them display a message asking for ransom money. The company is under attack and there is nothing you can do. Two years ago, that is what happened to the giant Danish company Maersk. The company has 80.000 employees and is presently number 262 on Forbes’ list of the world’s wealthiest companies. I don’t know, but I am guessing that Maersk had a state-of-the-art security system.
As a Norwegian journalist, I always read the yearly threat assessment report from the Police and the Intelligence service.
Both of them have for many years pointed at foreign intelligence gathering and cyber attacks as one of the biggest threats to national security and to Norwegian values. They are not talking about any homogenous group. Some of them can be business operatives wanting to get their hands on industrial secrets. Others can be uncouth criminals who are after credit card information or are extortionists. Still others can be intelligence officers ferreting around trying to find state secrets or mapping critical infrastructure. Or talented kids who are into “general motherfuckery”.
However, if the men behind the scene are a motley crew, it is still possible to sort what they are doing into three different categories.
Intelligence
Intelligence is in a way the low threshold activity. Foreign powers or business people find their way into servers and networks in order to spy. The aim can be to map and collect information about the defense and preparedness sector, government, business, research or crucial infrastructure. Intelligence gathering is something everybody is doing, but it shouldn’t be taken lightly. It can simply be the first stage in a three-stage rocket. The next stage is influencing maneuvers – and, if worse comes to worse – sabotage.
Influencing
Influencing is super trendy! Public and private actors make decisions that affect the interests of other countries or businesses. It is therefore useful to be able to influence these decisions. One can, as an example, imagine that the very large Maersk shipping network could be of interest for a builder of ports. Or that one major power or another have an interest in destabilizing and create divisions in Great Britain, just to take an absolutely wild example.
You have probably read an endless number of articles about this. The Cambridge Analytical scandal is an example. On order from Steve Bannon the company took advantage of a loophole in Facebook’s rules and used an inconspicuous app to gather user data from around 50 million users. These data were then used to influence voters in the American Presidential elections in 2016. Cambridge Analytica was also involved in the “Leave EU” campaign ahead of the Brexit referendum in Great Britain.
The Russian influencing actions directed at USA, EU and NATO are well-known. The somewhat unpleasant development is that China, that has traditionally been spying but not influencing, is cooperating more tightly with Russia and have probably become more active also in this field. The Australian parliament and parties, to mention one example, were recently hacked, just before a general election, probably by Chinese authorities.
Sabotage
Foreign powers and/or business actors plant complex encrypted virus hitting commercial activities or crucial infrastructure in society. That is what happened to Maersk. If that was a deliberate action to target Maersk, I really don’t know. Many signs point to it being a random incident. At Maersk it was the malware NotPetya that blocked the whole business. It could have been intended to be a Russian attack on Belarus activities, but went astray and ended up blocking 50.000 end points in 130 nations.
The only good thing one can say about targeted sabotage is that it is not very frequent. When directed at an enterprise, sabotage can prove costly, when directed at a society it can be categorized as an act of war. But there is a high risk of sabotage becoming more common in the future. In the last years digital sabotage has been tested in operations against European countries. Furthermore, the tools needed for sabotage have become cheaper and better so that smaller entities can be a serious threat as well.
Just watch out.
So … how to protect oneself?
Well, if you run a business, public or private, you should build a wall, to use a worn-out political phrase. You must upgrade your hardware and ensure that everything is updated. You cannot get around this. The problem is that it is not enough. You can have the safest data system in the world but still be letting intruders in.
Recently, I read a report from the data security company Proofpoint. They have found that the trend in the last two years has shifted from ransom money virus to espionage and theft of information. Because information and data are valuable stuff. The data that they find can both mean income and preparation for future attacks: And the most interesting thing about this is perhaps this: No intrusion or attack is being blamed on system error.
What is lacking in many companies is a security culture. Maybe the Head of IT shouldn’t have sole responsibility for security. Maybe the Head of HR should be on the track. Maybe all employees should be trained and be told that technology cannot always cover for them and be informed that they themselves are a considerable safety risk.
Proofpoint claims that 99 percent of the successful attacks are blamed on one employee or other who has been clicking thoughtlessly on an attachment, added sensitive information to a page on the net that looked trustworthy or has given away a password to someone who looked friendly.
The big, big majority of attacks are directed at man and man’s nature. Because the machines and the security systems are only one part of it, human beings the other. So, in the end there is one risk that is bigger than all the others: My stupid brain.

Joacim Lund
Technology commentator, Aftenposten
Years in Schibsted
14
My dream job as a child
Musician